What is cryptography?
Cryptography is the practice of keeping information secret, encrypting it in such a way that it cannot be decrypted within an acceptable period of time. Cryptography is very old and has an important function in the world of cryptocurrency. In this lesson, we will update you on the forms people have come up with over time and where we are today in this field.
Brief summary
✔️ Cryptography is the practice of keeping information secret, achieved by encrypting or hiding it in such a way that it cannot be decrypted by anyone without access to the proper key.
✔️ Cryptography has two types of keys: symmetric and asymmetric. Symmetric keys are used for everyday use and asymmetric keys, especially in cryptocurrency, have a public and a private key.
✔️ Cryptography has been used throughout history, such as in ancient Egypt and at the time of Caesar.
✔️ Cryptography has been used by governments and organizations to encrypt and decrypt messages, and it has traditionally been an important part of warfare.
Cryptography
Cryptography is the practice of keeping information secret. It is a compound of two Greek words, kryptos and graphein. Kryptos means hidden and graphein means writing or drawing. So you draw or write hidden messages.
What is acceptable effort?
The craft of cryptography involves encrypting or concealing information in such a way that an eavesdropping cryptanalyst cannot deduce from the data who the data subjects are and what information is being transmitted against acceptable effort.
For example, acceptable effort can mean deciphering it in days to decades. Unacceptable effort must involve numbers of years that people do not live, say a hundred years or more.
For example, it is known that if you create a complicated password with several different letters, numbers, capital letters and punctuation marks and make it a certain number of characters long that in a brute force attack (simply trying all possible combinations) it will take a powerful computer hundreds to thousands of years to guess the password. And this is what you guessed: this is an unacceptable effort!
Cryptographic keys
Cryptography is used to give only the sender and receiver the necessary keys and encryption so that no one can listen in.
Cryptography uses two types of keys: the symmetric variant and the asymmetric variant. In the symmetric variant, both sender and receiver have the same set of keys and the decryption key is known before the message is sent.
The asymmetric variant is most common in cryptocurrency. This involves a public and private key. The public key can be known to anyone, the private key is only in the possession of one person because it gives access to the coins themselves. Whoever has the private key can spend these coins.
First use asymmetric keys
This variant was first used by Diffie and Hellman. Before these two came up with this solution, couriers had to be used to deliver the decoder key, which of course was rather cumbersome and expensive.
Today, in companies and governments, the hybrid variant is most commonly used. The symmetric form for everyday use and the asymmetric variant to pass the private key. They do this because the asymmetric variant involves more processing power and therefore cost and is slower.
Well-known examples of cryptography
In ancient times, cryptography already existed because messages could be so important that only the recipient with the key had to be able to read what it said.
Cryptography in ancient times
In Egypt, some tombs have anomalous hieroglyphs. It is more than likely that it was some kind of secret writing that only people who knew what the key was could read.
The Kama Sutra also contains cryptography.
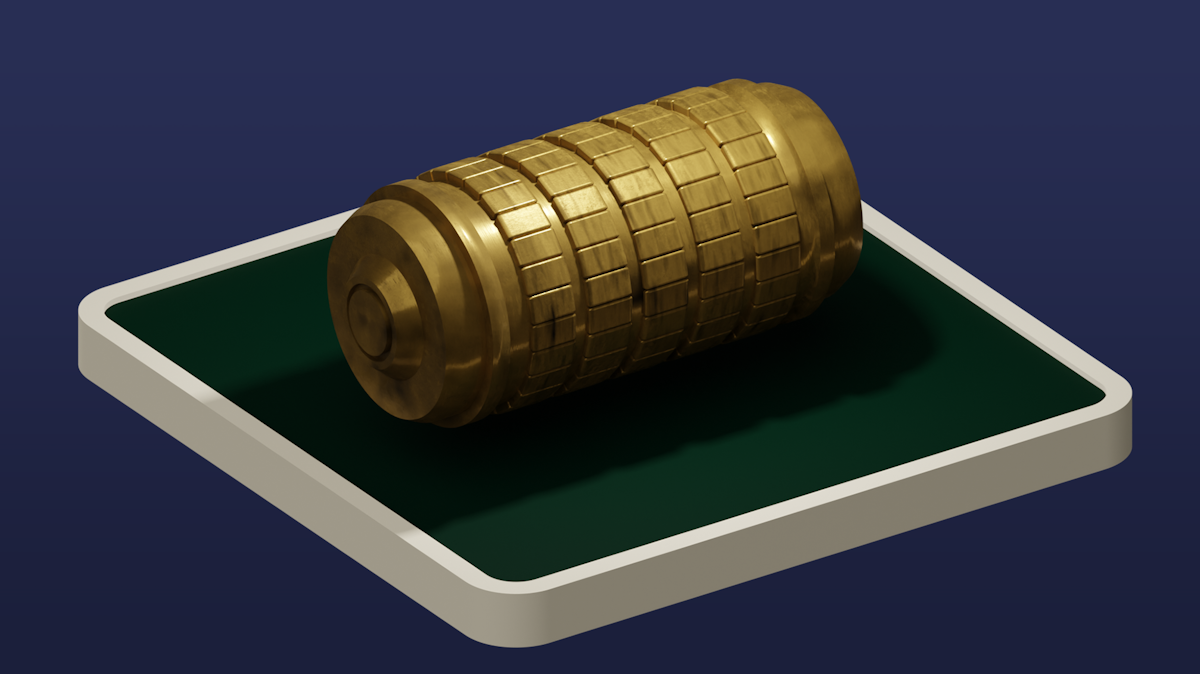
In his writings, the Greek writer Lysander discussed the scytale, which was used in the time of Alexander the Great.
Caesar could not be left behind then, although his Caesar cipher was fairly easy to decipher with frequency analysis. Caesar used a shifting of the letters by, say, 5 characters. A then becomes f, b becomes g, and so on. Because people know which letters are used the most, you could crack this system.
Famous secret codes
One of the most infamous stories about cryptography comes from the Babington betrayal. Babington's cryptography was broken by Phelippes. This contained the plot of Queen of Scots, Mary, against Queen Elizabeth 1 to assassinate her. She was therefore convicted of high treason.
The secrecy of Louis 14 was not broken for a long time.
In the 17th century, all major powers had their own "black room." These dealt with encoding and decoding messages. Napoleon was defeated with this, because Scovell had broken Napoleon's secret code and Wellington knew exactly what Napoleon was up to.
Cryptography in literature
Edgar Allan Poe popularized cryptography by writing about it in a magazine and later in his novella "The Golden Beetle."
Arthur Conan Doyle had Sherlock Holmes use cryptography to solve the riddle in "The Tale of the Dancing Men," where a pose gave a clue of the letter to be used.
Jules Verne and Dan Brown also used cryptography in their stories.
Enigma
A story that may be familiar to you is that of Enigma, the Germans' cipher machine, best known for the U-boats, which the British and Poles had deciphered.
Secret language is also used by parents when they share messages in a foreign language in the company of their offspring, when it is not intended for children's ears.
How does cryptography work?
Broadly speaking, cryptography works like this:
You want to send a message to another person but no one should know what's in it. That's plain text, or an understandable message.
You convert it into Ciphertext, which is a cryptographic representation in ciphertext. Without the necessary key, no one can read this text except the recipient, who holds the key.
The receiver uses his key to convert the Ciphertext into plain text. Now he can read the message.